Beyond the Patching Treadmill
Why Industrial Security Requires Architectural Invisibility
Key Takeaway: Siemens has appeared in over a dozen CISA advisories in early 2026 — not because of engineering failures, but because their massive market share creates an unavoidable attack surface. With unplanned downtime costing $260,000/hour and patch windows often stretching quarterly, traditional “patch and pray” security is failing. The solution isn’t better patching. It’s architectural invisibility that entirely eliminates the attack surface.
Photo by freepik
The Siemens Paradox: Market Dominance as Attack Surface
If you monitor CISA’s ICS advisories, you’ve noticed a pattern: Siemens keeps appearing. SINEC NMS. RUGGEDCOM. SIMATIC. SCALANCE. The advisory IDs pile up like shipping manifests. But this is actually a math problem, not necessarily a quality problem.
The industrial automation market has grown to an estimated $257.73 billionin 2026, with Siemens holding dominant positions in digital industries and smart infrastructure. When you’re the backbone of global manufacturing, every vulnerability you disclose has immediate implications for critical infrastructure worldwide.
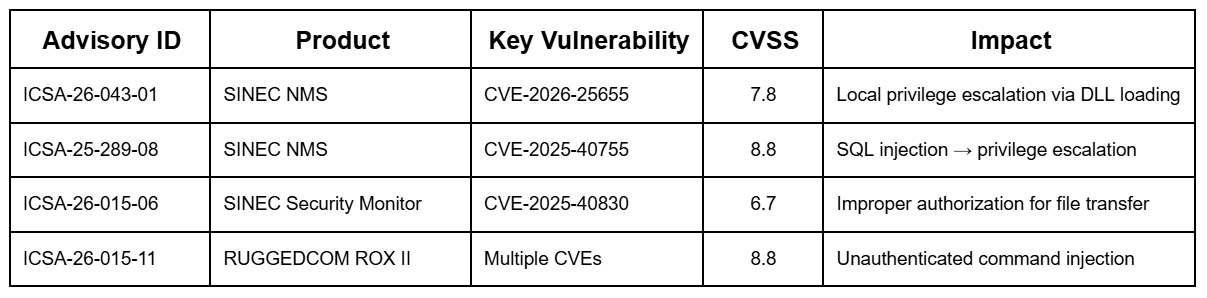
Recent High-Impact Advisories (Q1 2026)
The pattern reveals a strategic shift in attacker targeting. Rather than focusing solely on edge PLCs, threat actors are now targeting the management and monitoring layer, which is the software designed to secure the environment, and it is becoming the primary infection vector.
The Economics of the Patching Treadmill
The central tension that gets repeated over and over again is that CISA releases advisories, then vendors release patches, and finally, manufacturers, wait. . . often can’t deploy them?
2026 Downtime Costs by Industry
Sector Hourly Cost Reality Check
Semiconductor Fab | $10,000,000+ | A single contamination event wipes a week of production.
Automotive | $2,300,000 | One robotic cell failure stops the entire line.
Oil & Gas | $500,000 | Safety interlocks don’t negotiate with patch schedules.
Pharmaceuticals | $200,000 | Patching requires full process re-validation.
The average per hour cost across manufacturing is $260,000. Meanwhile, the average time from advisory to patch deployment — the “patch lag” — now stretches quarterly or longer for 85% of organizations.
The economic math doesn’t make sense. You can’t stop a $2.3M/hour production line to patch a vulnerability that might be exploited. So you don’t. And the window stays open.
The Compounding Problem
Cyberattack-induced downtime now averages 24 hours per incident which far exceeds typical maintenance windows. When an attack hits, it’s not just a brief interruption; it’s operational paralysis that lasts.
Attackers know the economic math, too. Nation-state actors like Volt Typhoonhave achieved 5-year dwell timesin US critical infrastructure, gaining entry from unpatched vulnerabilities, then patiently mapping OT networks while waiting for the right moment to act.
Why Traditional Security Models Are Failing
The VPN Illusion
CISA frequently recommends VPNs for remote industrial access. The logic seems sound: encrypt the tunnel, authenticate the user, protect the asset.
But VPNs have a fundamental architectural flaw: they require exposure to function.
A VPN gateway needs a public IP and open inbound ports which makes it a beacon for scanners
Once authenticated, users often receive broad network access, exactly the situation that lateral-movement attackers exploit
VPN appliances themselves become targets (see: Fortinet, Ivanti vulnerabilities 2025-2026) The VPN model is “trust, then verify.” In 2026, that’s backwards.
The Segmentation Struggle
Traditional network segmentation (VLANs, firewall rules) is theoretically sound but practically brittle in OT environments:
Interoperability demands: Mixed-vendor environments often require “flatter” networks than security teams would prefer.
Static rules: IP-based firewall rules can be bypassed once an attacker gains a foothold in a “trusted” segment.
Implementation cost: Redesigning network architecture requires significant downtime, which is the very thing manufacturers can’t afford.
The 2026 reality: perimeter defense is one-and-done. If an attacker bypasses the initial gate, there are few internal controls to stop lateral movement to the PLCs and switches that control production.
The 2026 Threat Landscape: Why This Is Urgent
Nation-State Pre-Positioning
The VOLTZITE group (linked to China’s Volt Typhoon) spent 2025 and early 2026 positioning within Western critical infrastructure. Their tactics:
Living-off-the-land (LotL): Using netsh, wmic, and PowerShell instead of custom malware
SOHO router compromise: The KV Botnet turns home routers into relay points
IT-to-OT lateral movement: Mapping network diagrams for future activation
These actorsare establishing long-term access for use during a potential geopolitical crisis, not just immediate disruption..
AI-Accelerated Reconnaissance: The Shrinking Window
In 2026, the most significant shift is the one that everyone sees, hears, and feels—speed. Why is this being felt so ubiquitously?
One reason is attackers now deploy AI-powered reconnaissance tools that can scan, identify, and classify exposed industrial systems in minutes rather than days. What used to require manual enumeration and expert analysis is now automated:
Automated CVE correlation: AI agents cross-reference exposed services with known vulnerabilities in real-time, prioritizing targets by exploitability
Credential inference: Machine learning models predict default and weak credentials based on device fingerprints and deployment patterns
Mass exploitation frameworks: Once a vulnerability is disclosed, AI-driven botnets can weaponize it and begin scanning globally within hours
The stats tell the same speed story. In 2024, the average time from vulnerability disclosure to active exploitation was 15 days. By late 2025, that window had collapsed to under 72 hours for high-value ICS targets. In 2026, we’re seeing exploitation attempts within 24 hours of CISA advisory publication.
This isn’t hypothetical. Shodan, Censys, and their darker equivalents now index industrial protocols in near real-time. An exposed SINEC NMS portal or RUGGEDCOM management interface can be discovered, fingerprinted, and added to an attack queue before your security team has finished reading the advisory.
The brutal truth is that AI makes offense faster while your main defense tools—patching—still happens at the same speed.
The February 2026 Hacktivist Surge
When Iran-US tensions escalated on February 28, 2026, over 60 Iranian-aligned hacktivist groups mobilized within hours, specifically targeting internet-exposed ICS devices across the United States.
Group Target Tactic
CyberAv3ngers Unitronics PLCs Default credential exploitation APT33 / Elfin Electric/Oil/Gas SCADA High-volume password spraying MuddyWater Telecoms & Energy Initial access broker operations Handala Hack Team Manufacturing MSPs Supply chain compromise
The attack surface mapping revealed that ports associated with industrial protocols — Port 102 (S7comm), Port 502 (Modbus), Port 44818 (EtherNet/IP) — remained widely accessible despite years of CISA warnings.
“Internet-exposed” is now synonymous with “compromised” during active conflict.
The Architectural Shift: From Defense to Unreachability
The Zero Trust model — “never trust, always verify” — is a prudent evolution from perimeter security. But for industrial environments, Zero Trust may not be enough.
The question isn’t “how do we verify every connection?”
It’s “why are we allowing connections in the first place?”
The Principle of Deterministic Unreachability
If a resource cannot be seen, it cannot be attacked.
Traditional industrial communication requires devices to listen for incoming connections on specific ports. These listening ports are the pathways attackers exploit. Every open port is an invitation. The architectural alternative: outbound-only connections.
No inbound ports listening = no attack surface to scan
No public IPs = no beacon for reconnaissance
Process-to-process tunnels = no network to traverse laterally
This isn’t defense-in-depth. It’s erasure of the attack surface entirely.
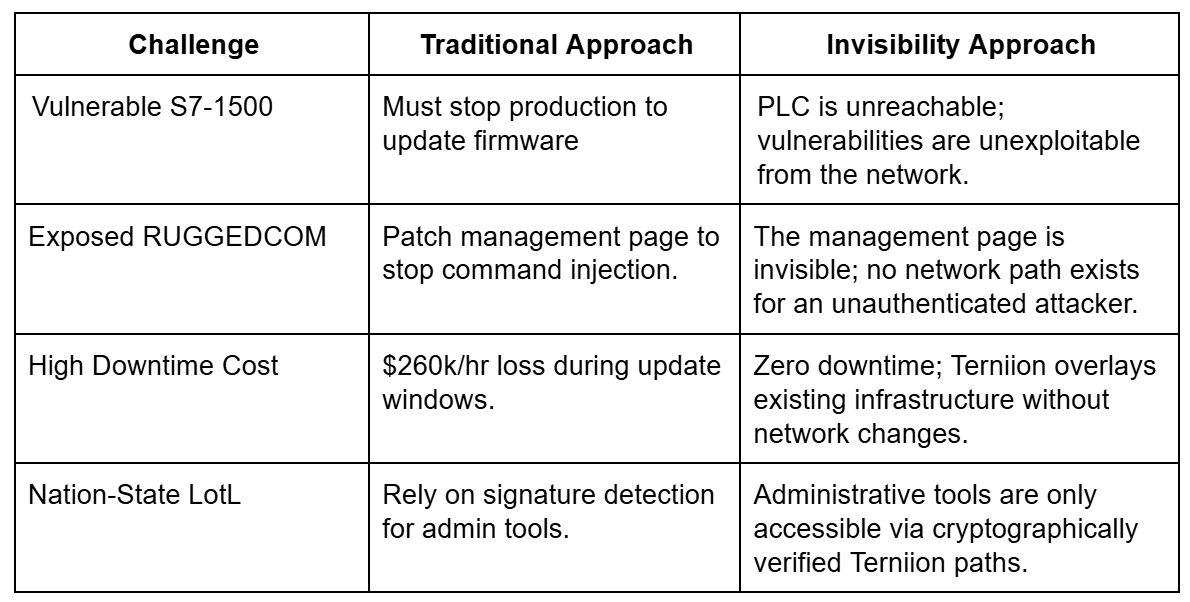
Securing Legacy Systems Without Patching
This architectural approach is most valuable where patching is most painful: legacy Siemens hardware that cannot be easily updated.
The key insight is that you don’t need to patch what can’t be reached.
Practical Steps Toward Infrastructure Invisibility
Step 1: Inventory and Exposure Assessment
Map every SIMATIC PLC, RUGGEDCOM switch, and SCALANCE access point. Use automated discovery to find any management interface reachable from the public internet — these are your highest-priority targets for “sealing.”
Step 2: Seal Critical Management Planes
Management systems like SINEC NMS are high-value targets because they provide control over the entire network. Deploy outbound-only access overlays to make management portals invisible to unauthorized scanners. Once verified, close inbound ports at the firewall.
Step 3: Implement Identity-Aware Access Control
Transition from IP-based trust to cryptographically verified identity. Every operator — internal technician or third-party vendor — must authenticate through the secure overlay, not just the network perimeter.
Just-in-Time (JIT) access: Provide temporary, least-privilege access for specific maintenance tasks. When the task completes, the tunnel dissolves — leaving no persistent path for attackers.
Step 4: Continuous Monitoring with Perfect Visibility
In an invisibility-secured environment, the network is “dark” to attackers but “crystal clear” to defenders. Every connection is a discrete, logged tunnel — making anomaly detection far simpler than monitoring the noise of a traditional flat network.
Clear data trend drives new strategies
The data from 2026 is unambiguous:
$260,000/hour downtime costs make patching windows economically prohibitive.
24-hour average cyber incident duration exceeds typical maintenance windows.
5-year nation-state dwell times mean attackers are already inside.
85% of organizations have quarterly-or-longer patch lags.
The patching treadmill is a recipe for operational failure. Traditional defense-in-depth assumed you could always run fast enough. In 2026, the treadmill is accelerating faster than anyone can sprint.
The only viable path forward is to make your infrastructure unreachable to eliminate the attack surface by erasing the network pathways. This allows you to stop running on the treadmill and step off it entirely. In a world where you cannot patch fast enough, the only solution is to ensure you cannot be seen at all.
References
• CISA ICS Advisories: cisa.gov/news-events/ics-advisories
• CISA Zero Trust Maturity Model: cisa.gov/zero-trust-maturity-model
• IBM Cost of a Data Breach Report 2024
• Deloitte Manufacturing Industry Outlook 2026