Autonomous Attack Paths: The Security Problem AI Is Creating
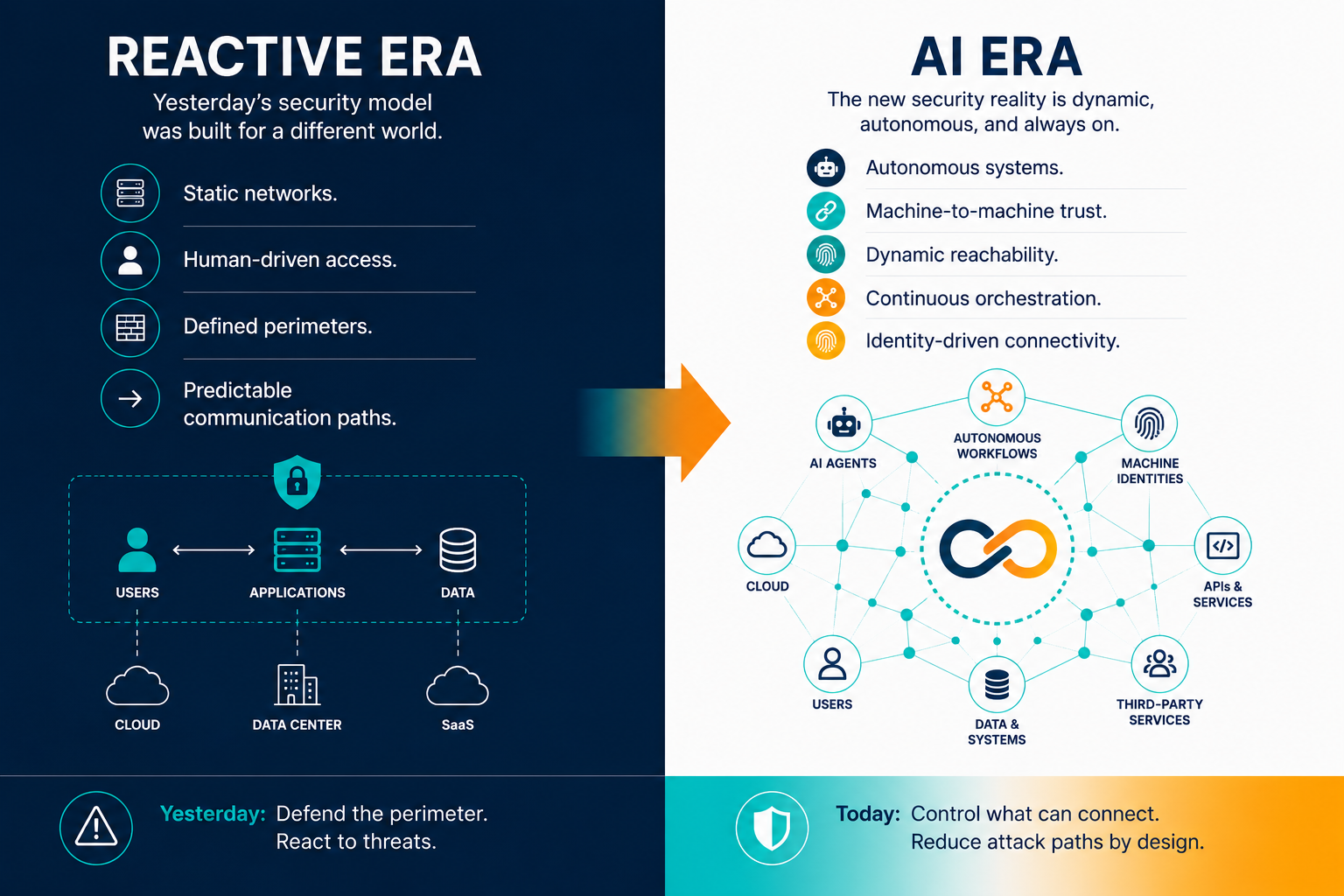
Traditional security was built for a world where humans initiated the actions that mattered. A user logs in, a browser makes a request, and a person clicks and authenticates. Security controls positioned themselves between those human actions and potential harm.
AI changes the initiator.
AI agents, copilots, autonomous workflows, and machine-driven orchestration now act on their own. Systems talk to other systems. Machine identities inherit trust, trigger processes, and chain actions across environments faster than any human response team can keep up.
The result is a new category of risk: autonomous attack paths.
When the Attacker Is a Machine
In the not-so-distant past, attack paths relied on compromised credentials, vulnerable endpoints, and lateral movement executed by an adversary operating at human speed. Detection had a fighting chance because the threat actor was constrained by the same clock as the defender.
Autonomous attack paths don’t operate on that clock.
They emerge through interconnected AI agents, machine identities carrying excessive permissions, API chaining, and inherited trust relationships that expand faster than any governance process can track. When an AI system acts on incorrect conclusions or gets compromised, it doesn’t wait for human review. It propagates. Across APIs. Across cloud environments. Across infrastructure that was never designed to contain it.
This is what the industry consistently underestimates. Hallucinations are no longer just content problems. When autonomous systems hold broad infrastructure access, a wrong output becomes an operational event.
The Trust Model That No Longer Holds
Most security teams understood their attack surface: human users, browser sessions, static trust boundaries, predictable network behavior.
Autonomous systems don’t operate inside those boundaries. They communicate continuously, orchestrate dynamically, and create connectivity paths that never appeared in the architecture diagram, because they weren’t human-initiated and never passed through controls built for human-initiated actions.
In many environments today, security teams have lost visibility into what autonomous systems can actually reach, which machine identities carry inherited trust, and where unintended connectivity paths exist. That’s not a configuration gap. It’s a structural one.
Organizations must move from reactive, perimeter-based security to preventive, deterministic security for the AI era.
Reachability Is the New Attack Surface
The detect-and-respond model was built for a world where perimeters held and human response times were acceptable. Autonomous infrastructure operates outside both of those assumptions.
When AI systems create dynamic connectivity paths and machine identities outnumber human users, detection is no longer a sufficient answer. The question shifts: what can these systems reach in the first place? Broad connectivity with implicit trust has been the default architecture of most enterprise environments. That’s now a liability rather than an operational convenience.
Reachability itself becomes the attack surface.
Containing What You Can’t Outrun
Securing autonomous environments demands a different architectural question. Not “how do we detect and respond faster?” but “what can autonomous systems reach, and how do we constrain it?”
That means limiting machine-to-machine connectivity to what’s operationally necessary. Enforcing identity-based trust at the process level, not the device or subnet level. Reducing the blast radius of any autonomous action, because propagation speed makes post-incident containment increasingly inadequate.
The organizations getting ahead of these issues aren’t layering more monitoring onto environments built for human-speed threats. They’re rebuilding for autonomous systems from the start to constrain reachability before any action is taken, rather than racing to contain propagation after the fact.
The next generation of security challenges won’t be defined solely by vulnerabilities. They’ll be defined by autonomous attack paths operating at machine speed. The architecture that contains them won’t be a faster version of what exists today.
Ready to Reduce Your Autonomous Attack Surface?
As AI systems become more deeply embedded in enterprise infrastructure, machine-to-machine trust, autonomous reachability, and identity governance become the new security fundamentals. Xiid builds infrastructure designed to contain autonomous attack paths before they propagate.
Learn how Xiid is helping organizations build unreachable-by-design infrastructure for the AI era.